Honeypots have long been a staple in the cybersecurity toolkit, serving as decoy systems designed to lure in attackers and study their tactics. However, in the ever-evolving landscape of cyber threats, the question arises: Are honeypots still useful in today's digital world? While the effectiveness of honeypots in modern cybersecurity may vary depending on the specific context and threat landscape, their value as a proactive security measure remains significant. This article delves into the relevance of honeypots in modern cybersecurity, exploring their effectiveness, benefits, limitations, and best practices for implementation. By examining their role in safeguarding digital assets against malicious actors, we aim to provide a comprehensive overview of how these deceptive systems contribute to a robust security posture.
 Introduction to Honeypots
Introduction to Honeypots
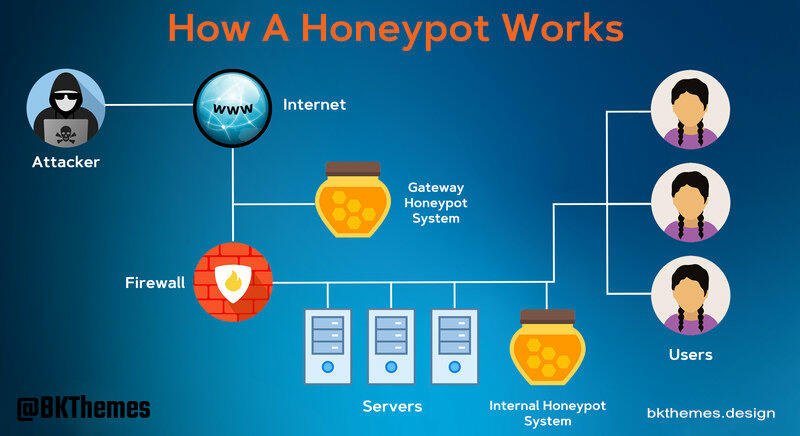
In the realm of cybersecurity, honeypots are deception tools designed to lure cyber threats and attackers. Unlike traditional security measures that aim to block attacks, honeypots are intentionally vulnerable systems or networks that act as bait. Their primary mission is to attract malicious actors, allowing security professionals to observe, analyze, and understand the tactics, techniques, and procedures (TTPs) used by attackers. This intelligence is invaluable for strengthening actual defenses, predicting future attacks, and developing more effective countermeasures.
The concept of a honeypot isn't new; it gained popularity in the early days of cybersecurity as a clever way to deceive and outsmart attackers. Back then, the digital landscape was less complex, and the threats, while serious, were often less sophisticated than today's advanced persistent threats. Honeypots provided a controlled environment to study attacker behavior without risking critical production systems. This historical context is crucial for understanding their evolution and how their utility has adapted to the modern, more intricate cyber battleground.
The Evolving Threat Landscape
The digital world has transformed dramatically, and with it, the nature of cyber threats. What began as individual hackers exploiting simple vulnerabilities has evolved into a complex ecosystem of state-sponsored actors, organized crime syndicates, and highly skilled independent attackers. The rise of Advanced Persistent Threats (APTs) marks a significant shift, as these groups are characterized by their stealth, persistence, and ability to bypass traditional security measures. APTs can remain undetected within networks for extended periods, exfiltrating sensitive data or preparing for disruptive attacks. Their sophisticated methods often involve custom malware, zero-day exploits, and intricate social engineering tactics, making them incredibly challenging to defend against.
Beyond external threats, the emergence of insider threats presents another critical challenge. These can be malicious employees, disgruntled former staff, or even unwitting individuals whose credentials have been compromised. Insider threats are particularly dangerous because they often bypass perimeter defenses, leveraging legitimate access to compromise systems or data. Furthermore, the proliferation of ransomware, supply chain attacks, and highly automated botnets means that organizations face a constant barrage of diverse and rapidly evolving threats. This dynamic environment necessitates a multi-layered security approach, where traditional firewalls and intrusion detection systems are complemented by more proactive and intelligence-gathering tools, such as honeypots. Understanding these evolving threats is key to appreciating where honeypots fit into a modern defense strategy, providing unique insights that other tools might miss.
Shopify growth support
Need help turning your Shopify store into a faster-selling machine?
This post is in Shopify, so here’s the most relevant next step if you want help applying it.
We help merchants improve store speed, custom functionality, theme quality, and conversion flow without turning the backend into spaghetti.
- Custom Liquid, theme, and app integration work
- Store optimization for speed, UX, and conversions
- Ongoing support for growth-stage Shopify brands
Honeypots in Modern Cybersecurity
Despite the sophistication of modern cyber threats, honeypots continue to offer significant value in today's cybersecurity landscape. Their primary strength lies in their ability to provide early warning and gather high-fidelity threat intelligence. By attracting attackers away from production systems, honeypots can detect reconnaissance activities, exploit attempts, and malware deployments that might otherwise go unnoticed. This allows security teams to observe attacker TTPs in real-time, understanding their motives, tools, and preferred attack vectors without risking critical assets. This intelligence can then be used to proactively patch vulnerabilities, update intrusion detection rules, and train security personnel, enhancing the overall defensive posture of an organization. For instance, understanding how attackers attempt to exploit common web vulnerabilities can inform better web development services and security practices.
However, the deployment and maintenance of honeypots are not without challenges. They require careful configuration and isolation to ensure that a compromised honeypot does not become a pivot point for attackers to reach legitimate systems. Furthermore, low-interaction honeypots, which simulate only a limited set of services, might not always fool sophisticated attackers, who can often detect their deceptive nature. High-interaction honeypots, while offering deeper insights into attacker behavior, carry a higher risk if not managed meticulously. The data collected from honeypots also needs to be analyzed effectively, often requiring integration with Security Information and Event Management (SIEM) systems to correlate events and extract actionable intelligence. Despite these complexities, when properly implemented and managed, honeypots serve as an invaluable component of a comprehensive cybersecurity strategy, offering a unique window into the minds and methods of adversaries.
Benefits and Strategic Deployment
The strategic deployment of honeypots offers several distinct advantages that complement traditional security measures. Firstly, they are a cost-effective source of threat intelligence. Instead of relying solely on external threat feeds, organizations can generate their own specific intelligence tailored to the types of attacks they are likely to face. This internal intelligence can reveal vulnerabilities unique to an organization's infrastructure or specific industry, providing a more targeted defense. Secondly, honeypots act as an excellent early warning system, alerting security teams to active threats before they reach critical systems. This proactive detection capability allows for faster incident response and mitigation, minimizing potential damage. Moreover, honeypots can serve as a training ground for security analysts, providing hands-on experience with real-world attack scenarios in a safe environment.
Effective honeypot deployment involves careful planning and consideration of several factors. Organizations often deploy a mix of low-interaction and high-interaction honeypots. Low-interaction honeypots are easier to deploy and maintain, suitable for detecting widespread scanning and automated attacks. High-interaction honeypots, while more complex, offer deeper insights into sophisticated attacker behavior and custom tools. It is crucial to isolate honeypots from production networks, typically placing them in a demilitarized zone (DMZ) or a dedicated segment. Robust logging and monitoring are essential, often integrating honeypot data with SIEM systems to correlate events and generate alerts. Furthermore, honeypots should be regularly updated and patched to reflect the latest vulnerabilities, making them more convincing targets. By integrating honeypots into a multi-layered security architecture, alongside firewalls, intrusion detection systems, and robust helpful content strategies for public-facing assets, organizations can significantly enhance their ability to detect, deter, and understand cyber threats.
Related resources
📧 Want to Stay Updated?
Get the latest web development tips and insights delivered to your inbox.